An Introduction to Passkeys: Why They Matter and How to Use Them
The cybersecurity world is buzzing with the news about Apple’s passkeys. An accessible way of going passwordless is a welcome change – even if it’s limited to just certain devices for now. With Google’s recent announcement that it supports passkeys on Chrome and Android, users can now opt into a beta to test the new feature. Even more recently, PayPal announced support for passkeys on Apple devices with iOS 16, iPadOS 16.1 or macOS Ventura.
With all this activity, it’s easy to wonder just what are passkeys — and why do they matter? More importantly, what do they mean for your business? This article will demonstrate how passkeys work, how they affect you, and how you can make a good decision about them for your business.
What are passkeys, and why do they matter?
Passkeys are an extended version of FIDO (Fast Identity Online) credentials. They streamline and package the benefits of FIDO for multi-device use within a single ecosystem. However, you can’t use passkeys between different ecosystems, nor can they extend trust to non-passkey devices or operating systems.
In simpler terms, passkeys use an existing protocol and web standard (FIDO and WebAuthn) to eliminate passwords. Instead of passwords, FIDO credentials are invoked with on-device authentication, like face recognition (e.g., FaceID) and fingerprint scanning (e.g., TouchID). FIDO has been around for a while, and passkeys make it easier to access for people already using the right operating systems — meaning only iOS 16 devices for now.
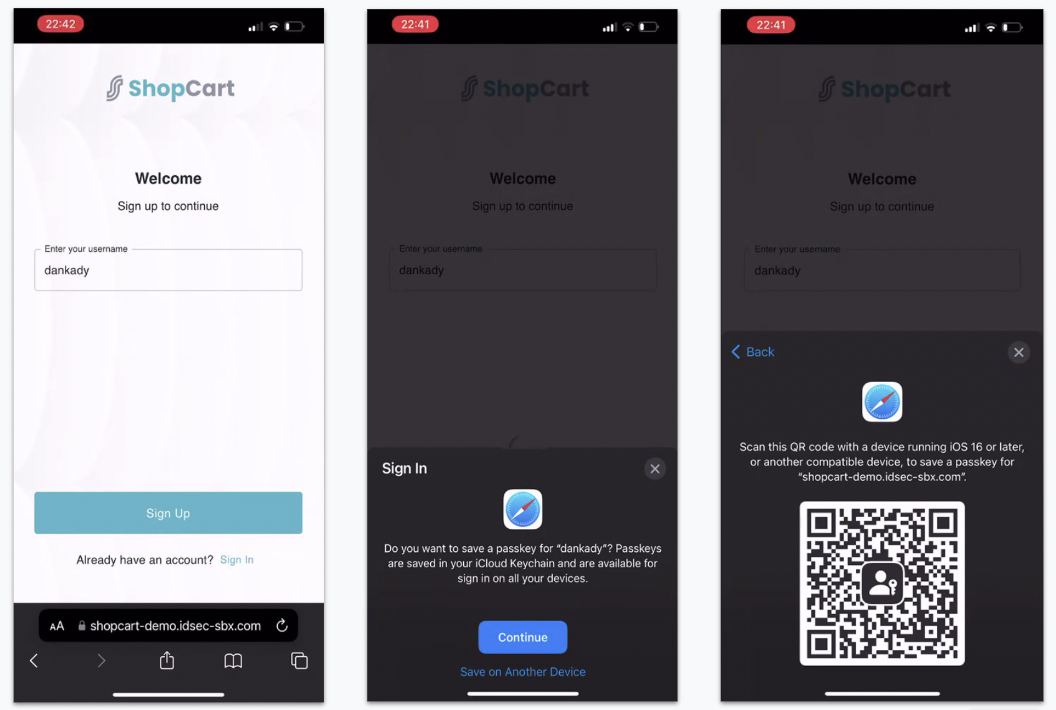
The user flow for using passkeys is relatively simple:
- The user enters a username that will be used for future logins
- A prompt, either on their device or via a QR code on another device, is shown for a biometric gesture
- A public-private key pair, which is the credential, is registered on the device
- On subsequent logins, the user enters their username and receives a prompt (on-device or via QR code) to answer a biometric challenge
Passkeys exist because passwords are on their way out. You don’t need to be a security expert to know that passwords have a laundry list of problems: poor usability, unreliable security, and costly upkeep. Half-measures like two-factor authentication (2FA) can reinforce passwords to a limited degree, but today’s companies want low-friction alternatives that customers will adopt.
Enter the FIDO Alliance, an industry association of security and tech firms working toward a passwordless future. With members like Google, Microsoft, Apple and Transmit Security, the FIDO Alliance represents a collective effort to make passwordless secure, open and consumable. They’ve been publishing passwordless architecture for nearly a decade, and the latest formulation, FIDO2, is the flagship protocol for passwordless solutions today.
The Web Authentication API, better known as WebAuthn, is a core component of FIDO2. WebAuthn is an official web standard that allows web services to offer easy cryptographic-based logins using biometrics, mobile devices, and FIDO security keys. However, FIDO credentials aren’t synced across devices, which prevents users from logging in on a new device without re-registering. As the protocol utilizing FIDO credentials, WebAuthn is limited to those available on the device.
To tackle this very specific limitation, the FIDO Alliance announced passkeys in collaboration with Google, Microsoft and Apple. All three have announced their intent to support passkeys. However, Apple has been the leading force behind passkey branding, and the company introduced the technology at the Apple Worldwide Developers Conference in 2022.
What are the benefits of using passkeys?
In simple terms, passkeys allow you to share FIDO credentials across multiple devices, solving the problems associated with lost or new devices. The first iteration of FIDO credentials isolated you to one device, but passkeys don’t have that problem. Passkeys are synced across devices via the cloud.
As an extension of FIDO credentials, passkeys work the same way on the back end and operate on the same protocols. Passkeys extend FIDO single-device credentials by enabling multi-device support, also known as multi-device FIDO credentials.
Users who enable passkeys go through one-time registration to generate a public-private pair of keys. The public key is stored on a web server. The private key is stored on the device. Users’ biometrics allow the private key to sign an authentication challenge to log in.
Typical FIDO scenarios never transmit private keys over the web, but passkeys can be shared across multiple devices via the cloud. It’s also possible to share the passkey from a nearby device with Bluetooth verification.
However, passkeys don’t include support for digital channels without FIDO platform support. They can’t extend to non-digital channels, such as non-FIDO desktop PCs, in-store environments, kiosks, or call centers. Additionally, because of the way passkeys can be transferred by utilizing cloud storage, they may not satisfy the security requirements of organizations like banks or financial institutions.
Does Transmit Security work with passkeys?
Yes! Transmit Security is a member of the FIDO Alliance Board and employs FIDO standards as one of the many authentication protocols we support. Keep in mind that passkeys aren’t a product or service. They are an extended version of FIDO credentials.
Think of our CIAM platform as an enterprise-grade wrapper around FIDO’s standards. Our platform is flexible enough to provide strong validation with or without passkeys, supporting both FIDO and non-FIDO devices. Regardless of the device, platform or ecosystem the user is a part of, they can still take advantage of the usability of passwordless authentication.
Transmit Security’s passwordless authentication APIs and SDKs utilize FIDO protocols, which means users authenticating to web services and applications from passkey-supported devices will benefit from everything passkeys can offer. To date, passkey device support is limited to iOS 16 devices with planned support for the upcoming release of macOS Ventura. Even after Google brings passkeys to Chrome and Android, this still leaves many consumers without passkey-supported devices.
Moving to passkey-only authentication would significantly limit a consumer base and is not recommended for any customer-facing login. Consider a user who is resistant to change and has opted out of passkey and biometric authentication. It’s essential to have the flexibility to support passwordless authentication through methods they prefer, such as magic link authentication or SMS OTP. These are all passwordless methods that are stronger than passwords.
The advantages of surpassing passkeys
Transmit Security’s platform services complement passkeys with proprietary cross-device capabilities and trust extension to non-passkey operating systems. We deliver proactive trust extensions to new devices and provide more flexibility than multi-device passkeys because our services don’t require a proximity check.
As an added security layer, we can also determine if the keys were generated on a specific device or shared via the ecosystem using passkeys. This allows organizations to choose how they want to implement and trust their users’ passwordless credentials.
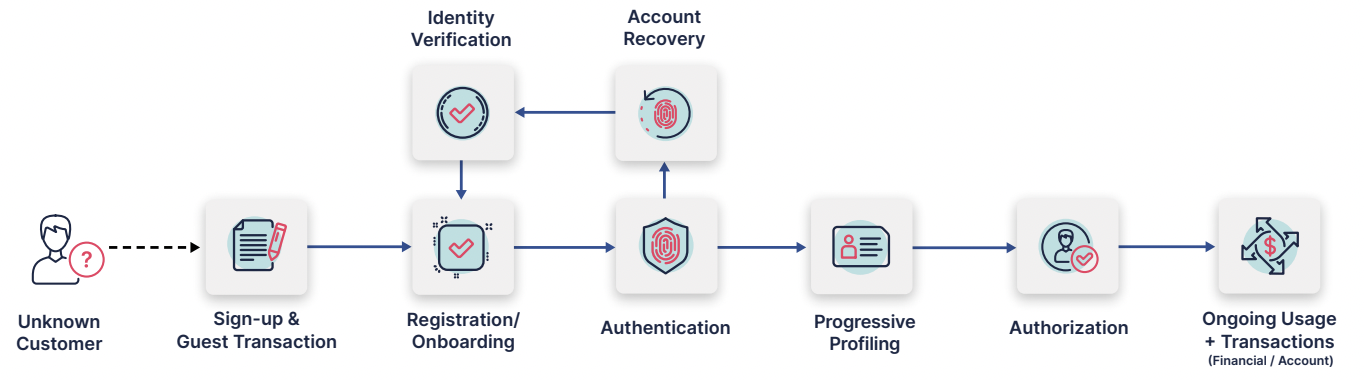
Authentication is just one of the requirements to manage ever-changing customer identities. Our scalable solution builds secure, trusted, end-to-end digital identity journeys across the user lifecycle. We cover the journey from registration to purchase and everything in between. We support your business beyond authentication with tools to manage sessions, assess risk, meet regulations, analyze logs, configure role-based access and more.
Learn more about how your business can leverage FIDO standards with the power of the Transmit Security CIAM Platform today.



