Traditional, password-based authentication is insecure. People commonly choose weak passwords or reuse the same password across multiple different accounts. This makes it easy for cybercriminals to guess or steal passwords, providing access to legitimate user accounts.
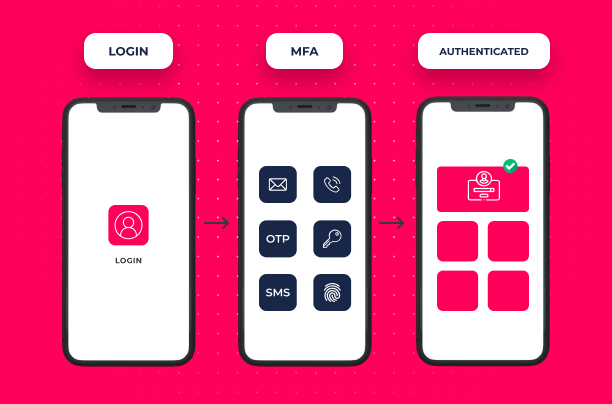
Multi-factor authentication (MFA) is designed to improve authentication security by requiring more than a password for authentication. If a password is weak or leaked, this isn’t enough for an account takeover attack. In this article, we answer what is MFA?

What are the three types of factors used in MFA?
Two-factor authentication (2FA) and multi-factor authentication (MFA) get their names from the fact that they require multiple different “factors” for a user to authenticate. 2FA requires two factors, while MFA requires two or more factors.
The factors used in MFA fall into three categories:
- Something You Know (Knowledge): Passwords are a prime example of a knowledge-based factor for MFA. This is a piece of information that should be kept secret and is typed into a computer to log into an account. Other common examples include PINs and passphrases.
- Something You Have (Possession): Authentication can also be based on possession of a particular object. A common choice is a smartphone, which can receive codes via text message, email, or an authenticator app using time-based one-time passwords (TOTP). The most common form of 2FA/MFA involves typing in such a code alongside a password. Other common possession-based factors include smartcards, physical tokens such as Yubikeys, or digital certificates stored on a device.
- Something You Are (Inherence): Inherence-based factors use biometrics for authentication. Common examples of this include fingerprint or facial recognition on smartphones. Other options include retinal scans, heart-rate monitoring, or anything else that is unique to a person.
A combination of knowledge-based and possession-based factors is the most common form of MFA. For example, a user may authenticate by entering a password (“something you know”) and a one-time passcode texted to their smartphone (“something you have”). To authenticate, a user needs to both know the password and have the phone, making this MFA.
However, other combinations are possible. For example, passwordless MFA combines possession-based and inherence-based factors. This could include using fingerprint recognition (“something you are”) to authenticate a user and reading an authentication token from a device (“something you have”).
Are all MFA factors equally secure?
No, different types of MFA factors offer different levels of security:
- Knowledge-Based: Knowledge-based factors like passwords are the most common because they are easy to implement. However, these factors are generally insecure because of the use of weak and reused passwords and the potential for passwords to be lost or stolen.
- Possession-Based: The security of possession-based factors depends on their implementation. For example, SMS-based MFA is less secure than a physical authenticator like a Yubikey because SMS messages can be intercepted via SIM swapping and other attacks. Also, possession-based authenticators have the risk of being lost or stolen.
- Inherence-Based: Biometrics is the most secure form of authentication because fingerprints, faces, etc. cannot be easily copied or stolen. Also, fingerprint or facial recognition is faster and easier for the user and doesn’t require them to have access to a particular device.
What are the benefits of MFA?
The primary benefit of MFA is improved account security. If an authentication system relies on a single factor, then an attacker only needs to learn or steal that factor. The use of multiple factors makes it more difficult for an attacker to successfully take over a user account.
However, the security benefits that an MFA solution provides depend on its implementation, the factors used, and whether or not it truly uses two distinct types of factors. For example, some websites use an emailed one-time code as a possession-based factor alongside a password. However, if the user authenticates to the email account using a password and if this password is the same as the other account, then both factors are actually knowledge-based and MFA provides no additional security.
What is adaptive MFA?
MFA provides additional security, but this can come at the cost of convenience in some cases. For example, a possession-based factor requires a user to have and use a physical device as part of the authentication process.
While the security benefits of MFA may be necessary in some cases, this may not always be the case. A company may decide that MFA is unnecessary in low-risk situations, but that the protection provided by multiple factors may be required in other scenarios. For example, password-based authentication may be acceptable when working from the office, but a remote worker may need the security provided by MFA.
Adaptive MFA makes this possible by allowing an organization to define rules for the authentication process. The user’s computer can provide contextual information (such as location and time of day) that can be used to determine risk levels. Based on the level of risk, an application could choose to forgo MFA or even require additional factors for extremely high-risk scenarios.
Combining MFA with SSO or SAML
Single sign-on (SSO) and the Security Assertion Markup Language (SAML) are other technologies designed to improve the security and usability of authentication systems. Instead of requiring a user to use different credentials to authenticate to different accounts, SSO and SAML allow a single authentication that provides access to multiple applications.
SSO and SAML can help to limit weak passwords and the burden of authentication, but an attacker that compromises a user’s SSO or SAML account has full access to linked accounts. By combining MFA with SSO or SAML, an organization can more strongly verify a user’s identity before providing them with access to multiple accounts.
MFA vs. Passwordless Authentication
MFA improves account security by bolstering a weak password with another authentication factor. However, this provides limited protection if both factors are insecure.
Passwordless authentication addresses the problem of insecure passwords by replacing a password with a non-password factor, such as “something you have” or “something you are”. Passwordless MFA combines the two concepts, using multiple non-password factors for user authentication.



