Applications connect today’s world. Customers want to use them because they’re easy to use and give on-demand services. According to research, US consumers used an average of forty-six different apps per month during the first half of 2021. Unfortunately, traditional customer identity and access management (CIAM) tools often fail to connect a person’s legal identity with their digital identity, using only an email and password to authenticate users. With portable digital identity, companies can give consumers control over personally identifiable information (PII) while still maintaining robust identity and access controls.

What is identity portability?
Given the number of apps that an average customer uses, creating secure credentials for each application is time-consuming, often leading to poor password hygiene. Identity portability gives people a way to create a single set of digital ID credentials that link their legal identity with their user credentials across multiple services.
A portable identity solution aggregates:
- Unique identifiers on a users device
- Legal documents verifying the person’s identity
- Biometrics, like face ID or fingerprints
What are the benefits of portable identity?
Portable identity offers customers and businesses the same benefits. Think of it as the mirror image. The business reduces risk while the customer has more control.
Privacy
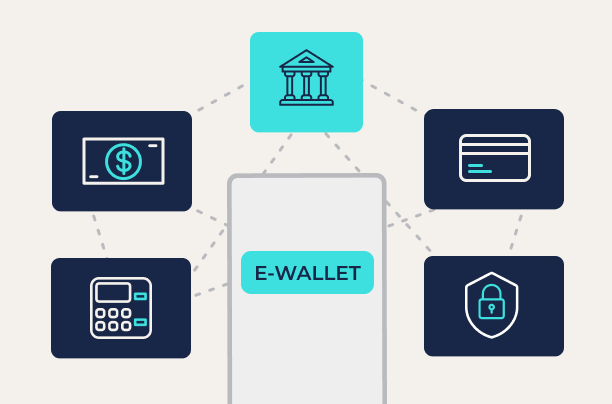
Portable identity gives people more control over their information. They can store their decentralized identifiers (DID) wallets on their smartphones. They don’t have to share PII with the business, giving them the control over their information that privacy laws require. The DID links the legal identity to the digital identity, so enterprises reduce the risk that cybercriminals will engage in fraudulent transactions.
Authentication
Multi-factor authentication (MFA) is fundamental to secure access. Portable identity prevents access unless an approved device is used. With portable identity, customers don’t need to enable MFA actively. They don’t have to worry about cybercriminals intercepting the security code sent in a text or email. The business is able to limit risks associated with credential-based attacks.
Re-usable
Password hygiene is a problem for both customers and businesses. Considering the average person uses 46 apps, people would need forty-six unique passwords. Most people won’t do that. Further, even those that do have good hygiene get frustrated when opening a password manager interrupts the login process. Meanwhile, businesses need to protect data from cybercriminals using stolen credentials or exploiting weak passwords. With portable identity solutions, users eliminate the need for passwords and can log into multiple apps with the same, secure DID.
What to look for in a portable identity solution?
Portable identity technologies give businesses and customers a way to protect themselves. When choosing to implement a portable identity solution, organizations should consider several capabilities.
Does it comply with FIDO2 specifications?
The FIDO Alliance sets standards for how a portable identity service manages:
- Cryptography
- Key storage
- Biometric storage
Solutions that meet the FIDO2 standards strengthen identity verification and provide enhanced secure account recovery.
Is it easy for the customer to use?
People aren’t going to adopt new technologies if it’s hard for them. A portable identity solution should be easy for users to install on their devices and make storing the required legal identity documentation simple.
Does it reduce identity stack complexity?
Identity is already challenging. Enterprise organizations often use multiple identity services, including:
- Identity governance and administration (IGA): granting and managing credentials and privileges
- Single Sign-On (SSO): allowing people to use a single account to authorize access
- Federation: bringing all identities into a single location to manage authorization and authentication
An organization should be able to reduce the complexity by using the portable identity solution for both workforce members and customers.
Securing Customer Access and Data with Portable Identity
Getting identity right ensures that businesses protect themselves and their customers. When customers feel confident that an organization is protecting their accounts, they are more likely to stay customers, ultimately leading to more revenue.
Transmit Security gives organizations a way to establish a passwordless experience for customers that reduces churn, with a seamless, cross-channel identity experience.
The same function applies for employees so that they have an effortless, secure workstation login to secure remote work. With identity as the perimeter, Transmit Security’s innovative technology reduces the security, privacy, and fraud risks associated with weak passwords.



