Cloud computing has exploded in recent years. Almost every organization is using cloud computing in some way, and many are planning to expand their cloud usage in the near future.
With the growth of the cloud came new models for consuming IT services. Everything is becoming an “as a Service” offering as cloud providers manage the underlying infrastructure for software, platforms, etc. for their customers.
As corporate IT infrastructure becomes more distributed between on-prem and cloud-based, managing user identity and authentication becomes more complex. Cloud Identity provides a solution to organizations looking to meet their expanding identity management needs.

What Is Cloud Identity and Cloud Authentication?
Cloud identity and cloud authentication are cloud-based solutions to organizations’ identity and access management (IAM) needs delivered via an “as a Service” model. The two main components of cloud identity and authentication are Authentication as a Service (AaaS) and Identity as a Service (IDaaS).
1. What Is Authentication as a Service?
Authentication as a Service (AaaS) is a cloud-based solution for user authentication. Online services can easily integrate AaaS into their applications, achieving strong and secure user authentication for distributed services. With AaaS, organizations can avoid a fragmented authentication experience by using a cohesive authentication service across all of their online applications.
2. What is Identity as a Service?
The move to the cloud also makes it more challenging for users to maintain online identities, which can easily become fragmented across different ecosystems. Identity as a Service (IDaaS) offers identity management under a service-based model. This enables users to maintain a consistent identity and user experience across all applications without application developers needing to implement and operate this solution in-house.
What Services Do Cloud Identity Providers Offer?
Cloud identity providers offer a few services, including:
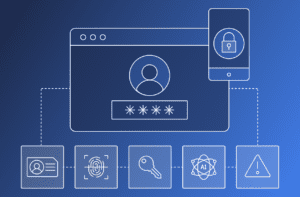
- Single Sign-On (SSO): SSO consolidates the authentication process to a single set of login credentials. After a user authenticates to the SSO provider, they can access any of the other accounts using the SSO service without needing to authenticate again.
- Multi-Factor Authentication (MFA): MFA requires a user to present multiple factors (password, biometrics, trusted device) to authenticate to a service. This makes it more difficult for an attacker to take advantage of a stolen password compromised via phishing or a data breach.
- Identity Management: Identity management involves tracking user identities and permissions across applications. This includes verifying a user’s identity, provisioning their account with the appropriate access and credentials, and performing authentication throughout the lifecycle of the account.
Examples of Cloud Identity
Several major tech companies have begun providing cloud identity. For example, many websites allow users to either log in with a username and password or login in with Google, Facebook, or Apple.
These services provide all of the core features of a cloud identity solution. Once a user has authenticated to their Google, Facebook, or Apple account, they do not need to perform additional logins. In many cases, these account providers support or require MFA as part of the login process. Finally, the service provider tracks the user’s account and provides identity and authentication data to third-party services as needed.
Cloud Authentication Solutions Help Businesses
Strong user authentication and access control are essential for modern businesses. Users’ account credentials are frequently compromised by phishing, data breaches, or the use of weak passwords. Online applications and services need to offer strong authentication options to protect themselves and their users.
Cloud authentication makes it much easier for companies to integrate strong authentication into their applications. Cloud identity providers often expose APIs that can be used to perform secure authentication with only a few lines of code, making authentication easier and more secure than custom implementations.